Introduction
Healthcare cybersecurity compliance today is defined less by policy alone and more by an organization’s ability to demonstrate HIPAA compliance in practice. Regulatory enforcement consistently evaluates whether safeguards meaningfully reduce risk to electronic protected health information (ePHI), focusing on technical implementation and operational outcomes rather than simple documentation. Covered entities are expected to integrate HIPAA compliance into daily operations, ensuring that every safeguard, from encryption to access control, is actively protecting patient data.
The Healthcare Cybersecurity Landscape: Persistent, High‑Impact Risk
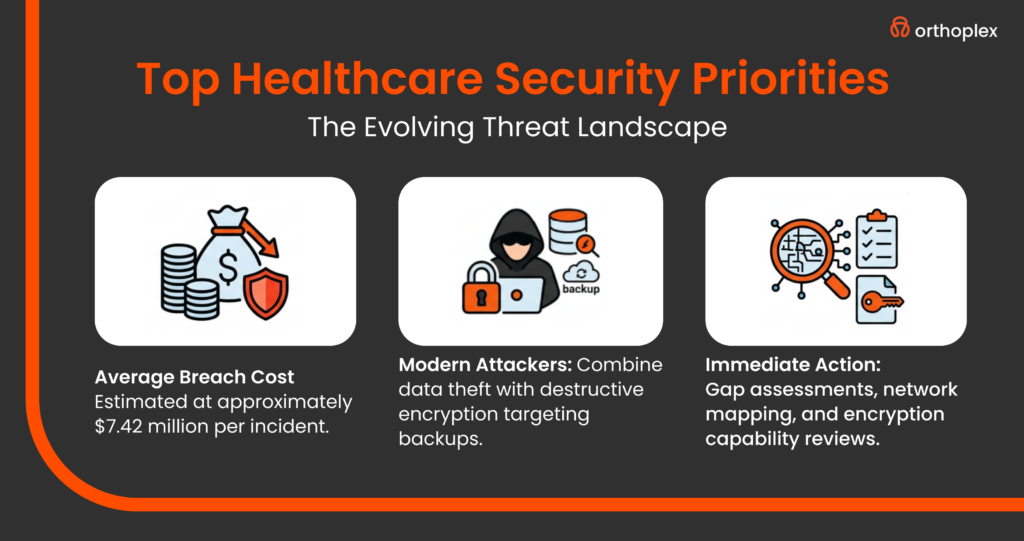
Healthcare remains among the most targeted sectors for cyberattacks, and breaches carry substantial financial and operational consequences. According to industry benchmarking, healthcare consistently experiences the highest average breach costs, with recent reports estimating approximately $7.42 million per incident (TechTarget, 2025). These incidents often have extended lifecycles, spanning detection, containment, and recovery periods, which directly impact patient care and operational continuity.
Large-scale disruptions, particularly those involving shared platforms or vendor services, demonstrate how a single compromise can cascade across multiple stakeholders, reinforcing the need for segmentation, containment, and verified recovery controls.
The threat environment has evolved beyond basic ransomware or encryption attacks. Modern attackers frequently combine data theft with destructive encryption, often targeting backups or secondary systems, which makes recovery more complex and increases regulatory expectations for demonstrable resilience. Healthcare organizations that cannot show effective containment and recovery procedures are at greater risk during enforcement reviews, highlighting that compliance is evaluated through practical effectiveness, not theoretical policy.
Interpreting the HIPAA Security Rule Through an Enforcement Lens
Today, the HIPAA Security Rule is interpreted primarily through the lens of operational effectiveness. Enforcement focuses on whether organizations can provide evidence that safeguards meaningfully protect ePHI under realistic threat scenarios. The Office for Civil Rights (OCR) emphasizes that all implemented controls should have measurable impact, and regulators assess not only the presence of controls but their consistency, completeness, and enforceability.
Technical safeguards, such as strong encryption, multi-factor authentication, centralized logging, and network segmentation, are considered baseline expectations for healthcare organizations of nearly any size. Alternative approaches can be accepted only if organizations demonstrate equivalent protection and provide clear evidence that risks are mitigated to the same degree as standard safeguards. Subjective interpretations or minimal implementations no longer satisfy enforcement expectations, and failure to operationalize these controls can result in significant compliance risk.
Encryption as a Foundational Control
Regulators now treat encryption as a core safeguard, not a discretionary option. Healthcare organizations are expected to implement encryption for ePHI both at rest and in transit, using widely recognized standards, and maintain exclusive control over cryptographic keys.
Enforcement attention is particularly strong on cloud-hosted systems and third-party platforms, where organizations must demonstrate that even providers cannot access unencrypted patient data without authorization. Demonstrating operational enforcement includes verifying that encryption covers all systems storing ePHI, cryptographic standards are properly configured, and key management processes, including generation, rotation, and separation of duties, are robust and routinely tested (NIST Guidelines, 2024).
Access Control and Authentication
Access control is evaluated based on real-world effectiveness in preventing unauthorized ePHI access. Multi-factor authentication is generally considered a baseline requirement, especially for remote administrative access and accounts with elevated privileges. Regulators also scrutinize emergency access procedures, password management policies, and device configuration standards to ensure they cannot be easily circumvented. The emphasis is on ensuring that access controls are practical, enforced, and auditable, protecting patient data under routine operations as well as during anomalous events.
Technology Asset Inventory and Network Visibility
Comprehensive visibility into technology assets and data flows is a cornerstone of modern enforcement. Organizations are expected to know not only where ePHI resides, but also how it moves across systems and networks, and which entities have access. Regulatory investigations have highlighted cases where failure to account for shadow IT systems, legacy platforms without security controls, or unmanaged vendor access contributed to systemic compliance gaps. Accurate and current asset inventories, along with detailed network maps, are considered essential evidence that organizations are actively managing and mitigating risk.
Risk Analysis as a Continuous Control
Risk analysis is one of the most scrutinized components of compliance. Regulators expect organizations to perform assessments that are methodical, written, and actionable, connecting findings directly to remediation activities. This includes reviewing all assets and data flows, identifying reasonably anticipated threats, evaluating the sufficiency of security measures, and determining both the likelihood and potential impact of vulnerabilities. Superficial or static risk assessments, even if documented, are insufficient; enforcement evaluates whether the process drives meaningful risk reduction and continuous improvement.
Business Associate and Ecosystem Accountability
HIPAA compliance extends beyond the boundaries of individual organizations. Business associates are expected to meet the same technical and operational standards as covered entities. Timely communication during security incidents, proactive monitoring, and evidence of coordinated response actions are key enforcement expectations. Insufficient oversight of vendors or delayed notifications can constitute systemic failures, reinforcing the principle that compliance is ecosystem-wide, not limited to internal operations.
The Implementation Imperative
Healthcare organizations cannot treat HIPAA compliance as a one-time initiative. Effective programs integrate cybersecurity into daily operational practice, ensuring that controls are exercised, verified, and continuously updated. Asset inventories, encryption coverage, access management, risk analysis, and business associate oversight must all be operationalized and demonstrable. Organizations that adopt a living, outcome-focused approach are better positioned to withstand audits, recover efficiently from incidents, and maintain patient trust, while those relying on documentation alone risk enforcement actions regardless of stated policies.
How Orthoplex Solutions Supports Healthcare Cybersecurity Compliance Readiness
Healthcare organizations require specialized technical expertise to implement proposed HIPAA Security Rule requirements and achieve comprehensive cybersecurity posture improvements.
Orthoplex Solutions provides development, cybersecurity, and cloud infrastructure services specifically designed to prepare healthcare organizations for regulatory compliance and security challenges.
Infrastructure Development and Compliance Preparation
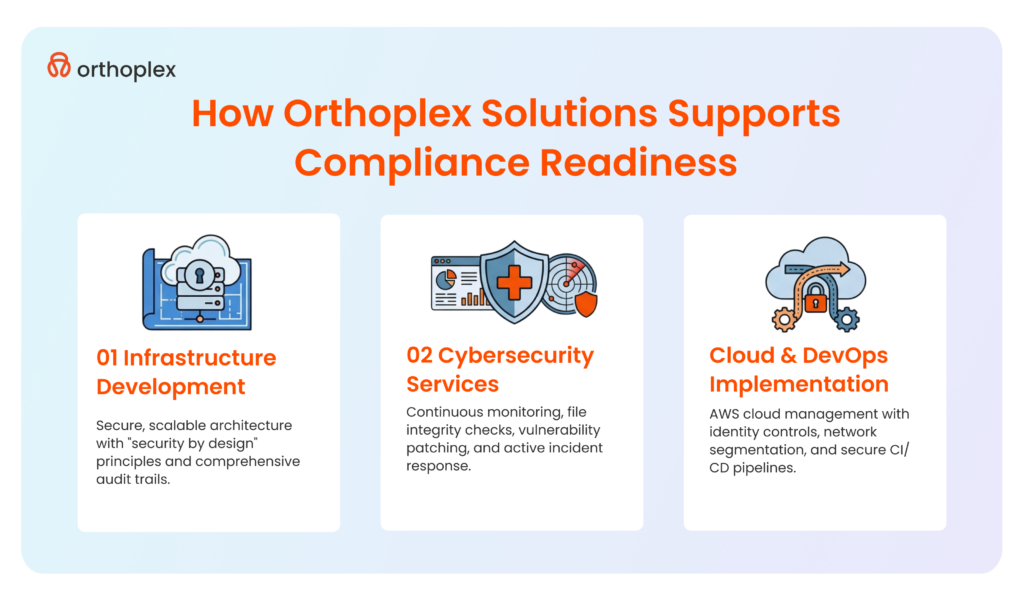
Orthoplex Solutions specializes in building secure, scalable infrastructure aligned with healthcare compliance requirements. The company’s development approach incorporates security by design principles, ensuring that applications and systems include appropriate technical safeguards from initial architecture through deployment.
This proactive approach reduces security gaps and positions organizations for rapid compliance when regulations finalize.
Web and mobile application development services address healthcare-specific requirements including ePHI handling, encryption implementation, access controls, and audit logging.
Orthoplex Solutions builds applications supporting clinical workflows while maintaining security standards necessary for HIPAA compliance. Applications include comprehensive audit trails documenting user activities, implement role-based access controls restricting functionality to authorized users, and encrypt data at rest and in transit using standards aligned with proposed HIPAA requirements.
The development process incorporates compliance documentation from project inception. Orthoplex Solutions maintains detailed system documentation including architecture diagrams, data flow documentation, security control descriptions, and implementation specifications.
This documentation supports healthcare organizations’ compliance demonstration efforts, providing the evidence necessary to satisfy regulatory audits and assessments.
Custom e-commerce solutions for healthcare organizations require specialized attention to payment processing security, prescription management, and patient data handling.
Orthoplex Solutions implements secure payment gateways meeting PCI DSS requirements, integrates prescription verification systems, and ensures that patient portals maintain appropriate security controls. These implementations enable healthcare organizations to offer digital services while maintaining regulatory compliance.
Cybersecurity Services and Continuous Monitoring
Orthoplex Solutions provides comprehensive cybersecurity services addressing proposed HIPAA Security Rule requirements. File Integrity Monitoring detects unauthorized modifications to critical system files, configurations, and ePHI repositories.
This capability identifies potential security incidents early, enabling rapid response before attackers can cause significant damage. File integrity monitoring supports compliance with proposed requirements for incident detection and response capabilities.
Vulnerability Monitoring and Patching services identify security weaknesses in organizational systems and applications. Regular vulnerability scanning detects known vulnerabilities in operating systems, applications, and network devices.
Orthoplex Solutions prioritizes vulnerabilities based on severity and exploitability, develops patching plans, and implements updates minimizing organizational risk while maintaining system stability. This service directly addresses proposed requirements for vulnerability management and risk mitigation.
Malware Detection capabilities identify malicious software attempting to compromise organizational systems. Advanced detection tools identify both known malware signatures and anomalous behaviors indicating potential zero-day attacks.
Rapid malware detection prevents ransomware encryption, data exfiltration, and other malicious activities that threaten ePHI confidentiality, integrity, and availability.
Active Response services implement automated and manual responses to detected security incidents. Automated responses quarantine compromised systems, block malicious network traffic, and disable compromised user accounts.
Manual response capabilities include incident investigation, forensic analysis, and remediation planning. These services ensure that organizations can respond effectively to security incidents, meeting proposed requirements for incident response capabilities and business associate notification timelines.
Cloud Infrastructure and DevOps Implementation for Healthcare Cybersecurity Compliance
AWS Cloud Management services optimize healthcare organizations’ cloud environments for security, compliance, and performance. Orthoplex Solutions implements cloud architectures incorporating encryption for data at rest and in transit, identity and access management controls, network segmentation, and comprehensive logging and monitoring.
Cloud configurations align with AWS best practices for healthcare, implementing services such as AWS Key Management Service for encryption key management and AWS CloudTrail for comprehensive audit logging.
CI/CD and Complete SDLC services establish secure development pipelines incorporating security testing throughout the software development lifecycle. Automated security scanning identifies vulnerabilities in application code, dependency libraries, and infrastructure configurations before deployment.
This approach prevents security weaknesses from reaching production environments, reducing organizational risk and compliance gaps.
Hosting and Maintenance services ensure that healthcare applications remain secure, available, and performant. Orthoplex Solutions implements redundant hosting architectures supporting business continuity requirements, maintains security patches and updates, monitors application and infrastructure performance, and provides 24/7 incident response capabilities. These services support proposed HIPAA requirements for system availability, integrity, and security.
Application and Server Monitoring provides visibility into system health, performance, and security events. Comprehensive monitoring detects anomalies indicating potential security incidents, identifies performance degradation affecting clinical workflows, and provides metrics supporting capacity planning.
Monitoring capabilities enable proactive problem identification and resolution before issues impact patient care delivery or create security incidents.
Integration and System Interconnectivity
Healthcare organizations operate complex technology ecosystems requiring secure integration between electronic health records, practice management systems, laboratory information systems, imaging systems, and countless other applications.
Orthoplex Solutions provides integration services ensuring that data flows securely between systems while maintaining appropriate access controls and audit trails.
EDI via AS2 implementation enables secure electronic data interchange for healthcare transactions including claims submission, eligibility verification, and remittance advice. AS2 protocol implementation incorporates encryption and digital signatures ensuring transaction confidentiality and integrity.
This capability supports secure business associate communications while maintaining compliance with transaction security requirements.
ERP and CRM integration connects healthcare business systems with clinical applications. Orthoplex Solutions implements integration architectures maintaining data consistency across systems, implements appropriate access controls restricting ePHI visibility to authorized applications and users, and ensures that integration points include comprehensive logging supporting audit activities. These integrations improve operational efficiency while maintaining security and compliance.
Third-party API integration enables healthcare organizations to leverage external services including laboratory result delivery, prescription routing, and patient engagement platforms.
Orthoplex Solutions implements secure API connections incorporating authentication, encryption, and rate limiting. API integrations include error handling and failover capabilities ensuring system resilience when external services experience disruptions.
Data migration and manipulation services support healthcare organizations transitioning between systems or consolidating data from multiple sources. Orthoplex Solutions implements secure migration processes maintaining data confidentiality during transition, validates data integrity after migration, and provides comprehensive documentation supporting compliance requirements.
These services enable technology modernization initiatives while maintaining regulatory compliance throughout transition periods.

The Orthoplex Approach to Healthcare Cybersecurity Compliance Support
Orthoplex Solutions recognizes that healthcare compliance represents a shared responsibility between development teams and healthcare organizations. Technical infrastructure, development processes, and documentation provided by Orthoplex Solutions prepare the foundation for compliance.
However, healthcare organizations retain ultimate responsibility for content management, clinical workflows, and business processes that fall outside technical implementation scope.
The Orthoplex compliance preparation approach focuses on controllable technical elements including secure application architecture, encryption implementation, access controls, audit logging, vulnerability management, and infrastructure security.
These elements create compliance-ready platforms that healthcare organizations can leverage for regulatory purposes. Orthoplex Solutions provides comprehensive technical documentation describing implemented security controls, supporting healthcare organizations’ compliance demonstration efforts.
Healthcare organizations remain responsible for elements outside technical implementation including clinical content accuracy, workflow appropriateness, business process compliance, organizational policies and procedures, and workforce training and awareness.
Orthoplex Solutions collaborates with healthcare organizations to ensure that technical implementations support organizational compliance requirements while recognizing the distinct responsibilities each party maintains.
This collaborative approach enables healthcare organizations to leverage specialized technical expertise for infrastructure and application development while maintaining appropriate oversight and control over clinical and business processes.
The partnership model ensures that organizations receive compliance-ready technical solutions without creating inappropriate dependencies or delegating responsibilities that must remain with covered entities under regulatory requirements.
Preparing Your Organization for Audit Success
Healthcare organizations face increasing regulatory scrutiny as breach rates and costs escalate. Organizations must prepare comprehensively for potential audits, ensuring that security programs include not only technical controls but also documentation, policies, procedures, and workforce training supporting compliance demonstration.
Documentation Requirements and Evidence Collection
Comprehensive documentation forms the foundation of successful audit outcomes. Organizations must maintain evidence demonstrating security program implementation including technology asset inventories, network maps, risk analysis documentation, security policies and procedures, business associate agreements, incident response plans and procedures, disaster recovery and business continuity plans, and workforce training records.
This documentation should be readily accessible, current, and complete.
Technology asset inventories must include all devices, applications, and services that handle ePHI. Documentation should specify asset locations, responsible parties, operating systems and software versions, network addresses, and security control implementations.
Organizations should maintain inventory update records demonstrating compliance with annual review requirements and updates following environmental changes.
Risk analysis documentation represents one of the most scrutinized elements during audits. Organizations must demonstrate systematic risk identification, vulnerability assessment, threat evaluation, and mitigation planning.
Risk analyses should include specific findings regarding identified risks, evaluated likelihood and impact, implemented or planned mitigation measures, and residual risk acceptance decisions. Documentation should demonstrate that risk analyses inform security investment decisions rather than serving merely as compliance exercises.
Security policies and procedures must comprehensively address administrative, physical, and technical safeguards. Policies should establish organizational security requirements, define roles and responsibilities, and specify compliance expectations.
Procedures should provide detailed implementation guidance enabling workforce members to perform security activities consistently. Organizations should maintain records demonstrating periodic policy review and updates addressing environmental changes, technology evolution, and regulatory modifications.
Workforce Training and Awareness Programs
Workforce training represents both a regulatory requirement and a practical necessity for security program effectiveness. Human error remains the leading cause of security incidents, with 42% of healthcare ransomware attacks traced to insufficient staffing and 41% to known security gaps that organizations failed to address.
Comprehensive training programs reduce these risks by ensuring that workforce members understand security requirements, recognize potential threats, and respond appropriately to security incidents.
Training programs should address role-specific security responsibilities including general security awareness for all workforce members, technical security training for IT personnel, privacy training for workforce members handling ePHI, incident response training for security team members, and leadership training for executives and board members.
Training should occur upon hire, annually, and following significant security incidents or policy modifications.
Security awareness programs should address common attack vectors including phishing recognition and reporting, password security and management, mobile device security, social engineering tactics, and physical security requirements.
Healthcare organizations should implement simulated phishing campaigns testing workforce recognition and response, providing additional training for individuals demonstrating vulnerability to these attacks.
Organizations should maintain comprehensive training records documenting completion dates, training content, and assessment results. These records demonstrate compliance with regulatory requirements and support corrective action when workforce members fail to meet security expectations.
Training programs should evolve continuously, incorporating lessons learned from security incidents and addressing emerging threats.
Continuous Compliance Monitoring and Improvement
Healthcare cybersecurity compliance represents an ongoing process rather than a one-time achievement. Organizations must implement continuous monitoring capabilities identifying compliance gaps, security weaknesses, and control failures requiring corrective action.
Monitoring programs should include periodic self-assessments evaluating security control effectiveness, vulnerability scanning identifying technical weaknesses, security metric collection and analysis, and regular leadership reporting.
Self-assessment programs should follow structured methodologies evaluating compliance across all regulatory requirements. Organizations can leverage HIPAA Security Rule checklists, NIST Cybersecurity Framework assessments, or similar tools ensuring comprehensive evaluation.
Self-assessments should occur at least annually, with more frequent assessments in high-risk areas or following significant environmental changes.
Security metrics provide objective evidence of program effectiveness and identify trends requiring attention. Organizations should collect and analyze metrics including vulnerability remediation timelines, incident response times, security training completion rates, unsuccessful authentication attempts, malware detection and remediation, and patch compliance rates.
Metrics should be reported regularly to leadership, enabling informed decision-making regarding security investments and priorities.
Continuous improvement processes incorporate lessons learned from security incidents, assessment findings, and industry developments. Organizations should conduct after-action reviews following security incidents, identifying root causes and implementing corrective actions preventing recurrence.
Assessment findings should translate into action plans addressing identified gaps within defined timelines. Industry developments including new threats, attack techniques, and regulatory changes should prompt security program updates ensuring continued effectiveness.
Conclusion: Taking Action for Healthcare Cybersecurity Compliance Today
The proposed HIPAA Security Rule modifications represent the most significant regulatory changes in over a decade, fundamentally reshaping healthcare cybersecurity expectations. Organizations must recognize that healthcare cybersecurity compliance preparation cannot wait for rule finalization.
The escalating threat environment and mounting breach costs demand immediate action regardless of regulatory mandates. The proposed 180-day implementation timeline following finalization leaves minimal margin for delay.
Healthcare organizations should initiate gap assessments immediately, evaluating current security postures against proposed requirements. Technology asset inventories and network mapping exercises provide foundational visibility necessary for comprehensive risk analysis and security planning.
Encryption capability assessments identify systems requiring implementation or upgrade to meet mandatory standards. Access control reviews determine multi-factor authentication deployment requirements and network segmentation needs.
Leadership commitment remains essential for successful implementation. Executive teams must allocate sufficient resources, establish clear accountability, and communicate implementation priorities throughout organizations.
Board-level oversight ensures that security investments receive appropriate attention and that risk decisions align with organizational risk tolerance. Security program success requires organizational commitment extending far beyond IT departments to encompass clinical, operational, and administrative leadership.
The proposed HIPAA Security Rule modifications align with cybersecurity best practices that organizations should implement regardless of regulatory requirements. Enhanced encryption, comprehensive access controls, systematic risk analysis, and continuous monitoring represent fundamental security capabilities necessary to protect ePHI in current threat environments.
Organizations implementing these capabilities position themselves not only for regulatory compliance but also for operational resilience and patient trust preservation.
Healthcare cybersecurity compliance readiness requires ongoing commitment rather than one-time project completion. Threat landscapes evolve continuously, technology environments change, and regulatory expectations increase over time.
Organizations must establish programs supporting continuous assessment, improvement, and adaptation. Regular self-assessments identify emerging gaps, security metrics provide objective performance evidence, and continuous improvement processes incorporate lessons learned from incidents and industry developments.
Organizations seeking specialized expertise for healthcare cybersecurity compliance implementation can leverage Orthoplex Solutions’ comprehensive service portfolio, including development, cybersecurity, cloud management, and integration capabilities.
Technical infrastructure preparation positions healthcare organizations for audit success while maintaining focus on patient care delivery and clinical excellence. The partnership between specialized technology providers and healthcare organizations enables effective security program implementation without diverting clinical resources from essential patient care activities.
The time to act is now. Healthcare organizations that begin implementation immediately position themselves for successful compliance, reduced breach risk, and enhanced patient trust. Those that delay face compressed timelines, resource constraints, and increased vulnerability to attacks that threaten both regulatory compliance and patient safety.
Healthcare cybersecurity compliance represents not merely a regulatory obligation but a fundamental responsibility to patients who entrust organizations with their most sensitive information.




